Join us at hack.lu 2025 — Info & Registration
Duration: 30 min
Type: Talk
Speakers: Hugo
Abstract
As CI/CD pipelines become integral to modern software development through systems like Azure DevOps or GitHub Actions, and tools such as Terraform and Ansible, their compromise can have devastating effects, from infrastructure breaches to mass malware distribution.
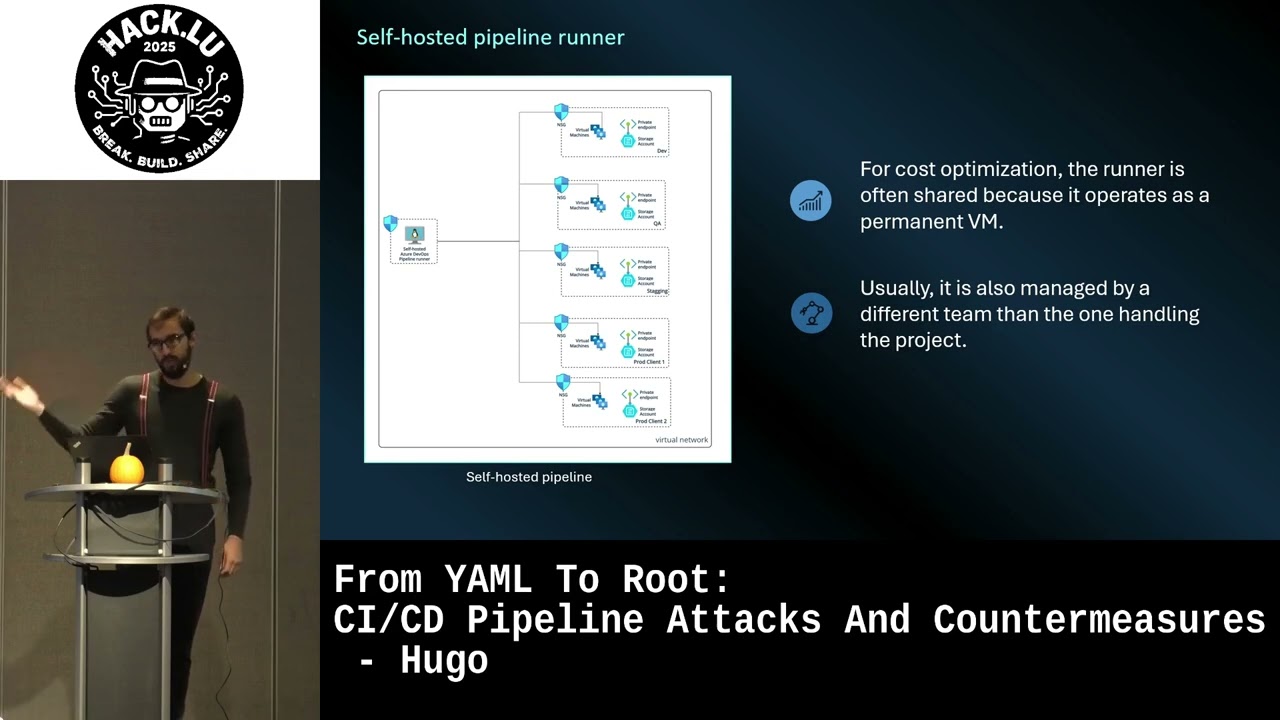
Originally, CI/CD pipelines were managed and accessed only by a limited group of administrators or integration engineers. However, with the widespread adoption of Infrastructure as Code, it has become increasingly common for companies to open controlled access to their pipelines—sometimes even to external clients. This shift supports use cases such as self-service sandbox environments, client-controlled infrastructure provisioning, or dynamic testbed deployments in multi-tenant platforms. While these scenarios offer flexibility and scalability, they also introduce new risks and potential attack vectors, making it critical to rethink pipeline security under this broader exposure model.
In this talk, we will demonstrate how an attacker can exploit seemingly limited permissions—such as those of a standard contributor account—to fully compromise a CI/CD pipeline and the underlying infrastructure. By chaining misconfigurations, abusing legitimate features, and bypassing common restrictions, we’ll show how limited access can quickly escalate into full control.
In the second phase of the talk, we’ll look at the defensive side: how a company can effectively secure its pipelines in a context where access is no longer limited to internal teams.
Description
Talk Description and Structure
The talk is divided into two main parts: an offensive demonstration and a defensive strategy session.
Part 1 – Offensive: From Contributor to Full Compromise
We will begin with a realistic demonstration of attack scenarios showing how a basic contributor-level account can be used to hijack a CI/CD pipeline, escape the provided use cases and fully compromise the infrastructure through Terraform integration. To reflect real-world conditions, common pipeline protections will be enabled—and bypassed. Key topics include:
-
Remote Code Execution via pipeline files:
We’ll explore how attackers can achieve RCE through configuration file manipulation or config file poisoning, Terraform constructs (e.g.,
externaldata sources, malicious custom providers or modules, abuse of provisioners), and other legitimate pipeline features. -
Bypassing restrictions:
Techniques to bypass provider restrictions, function or module blacklists, and CI/CD step filters will be demonstrated, showing how misconfigurations or insufficient validation open the door to exploitation.
-
Post-exploitation steps:
Once initial execution is achieved, we’ll show how attackers can perform lateral movement in the underlying infrastructure, such as:
- Extracting sensitive secrets (cloud credentials, environment variables, connection strings).
- Establishing persistence within the CI/CD pipeline (e.g., malicious jobs, trigger abuse, backdoor artifacts).
Part 2 – Defensive: How to Secure Your Pipelines in This New Model
With the offensive risks clearly laid out, we’ll move on to the defensive strategies. This section is divided into two phases:
-
Reinforcement and Protection:
This proactive phase aims to secure the pipeline by design. We’ll cover:
- Secure handling of secrets and credentials.
- Hardening of CI/CD agents and build runners.
- Implementation of integrity checks (e.g., checksum validation, signed commits, restricted runners).
- Tightening access control and repository hygiene.
-
Detection and Monitoring:
Even well-protected pipelines require active monitoring to catch suspicious activity. We’ll discuss:
- CI/CD log analysis techniques.
- Indicators of compromise in pipeline behavior.
- Anomaly detection approaches tailored to build systems.